The Purpose Driven IAM Life
[Cross-posted from the Identropy blog, where I will be contributing some posts from now on]
Another Catalyst conference (now Gartner Catalyst) has come to an end with the former Burton Group analysts challenging us once more to do better as an industry. It’s an unfortunate reality that cost overruns, unrealized benefits and missed objectives still plague most customers of identity management solutions. While there are still things we need to do on the technology side of the equation (most notably, moving towards a pull-based identity architecture in our application and platform layers), there is much more we can do in a more immediate fashion on the business and deployment side of identity management. And since any new proposal must be accompanied by an appropriate buzzword, here’s the one I took away from Catalyst – fit-for-purpose (putting $1 in the Bob Blakley piggybank).
For a while now, it’s been fashionable to bash provisioning. But to me, this was always misguided anger. Yes, it’s true that many provisioning projects suffer from missed deadlines and budget woes. But that was never because of the technology, which did exactly what it was supposed to (though there is still much we can do to improve it’s maturity and stability). It was always because of the way it was sold, deployed and mismanaged. How often did we hear massive provisioning projects being drafted to achieve regulatory compliance, only to find out that it wasn’t a sufficient control? How many connector development projects were defined to automate provisioning to many 100s of targets, without any ROI calculations ever being done to determine it’s value to the business (though it’s value to the implementing SI was all too obvious)?
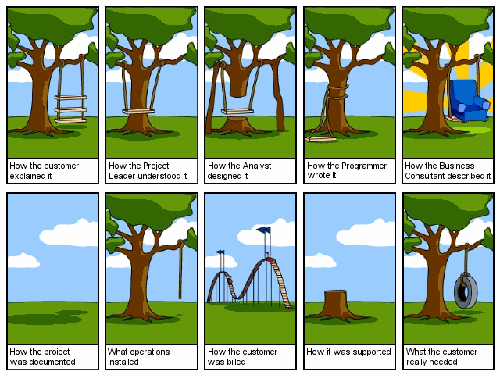
The angst has gone so far as to create a whole new market – Identity & Access Governance (IAG) – and marketing terms like “next generation provisioning”. But there is nothing revolutionary (or even evolutionary) about the model of automating provisioning to your most sensitive and/or high volume targets, while only setting up approval workflows and manual provisioning for the rest. You could do this with Thor’s Xellerate provisioning product (now Oracle Identity Manager) back in 2003, when we created full fledged functionality for manual provisioning that included email notifications and a provisioning task list (with detailed data and instructions) for your IT admins. Through all the noise and FUD, what is actually coming to the fore is the deeper and more relevant concept of understanding exactly what your use cases are for your IAM deployment, and focusing the features, design and deployment on meeting those use cases.
The most successful IAM projects have always done exactly this, with plans that classified their applications into tiers corresponding to the controls they wanted to put in place, creating role management projects that emphasized defining only the higher value business roles instead of trying to blanket everyone in the enterprise, and finding the right blend of automated controls, manual decision-making and oversight mechanisms. The defining characteristic in these projects was always an attitude of rational, measured response to the risk involved – in other words, an emphasis on making sure that any solution rolled out was fit-for-purpose.
This is the philosophical approach to IAM that attracted me to Identropy, where it exists both in the advisory and implementation aspect of our business, and in our approach to designing SCUID Lifecycle. Lifecycle is not meant to be all things to all people. It’s meant to be exactly what is needed for the majority of customers out there. We’ve used our years (decades?) of expertise in this space to come up with just that measured set of features and use cases, and will continue to refine them in conjunction with our customers. That is the part that excites me most about this new journey I’ve started. And I’m glad that Lori, Bob and the rest of the Catalyst gang validated our core belief for us.

In this blog post of notes from the 2012 Gartner IAM Summit http://360tek.blogspot.com/2012/12/gartner-iam-notes.html says that IAM and IAG seem to be converging. What does this mean for my organization? We are an Identropy customer that will soon move from Aveksa to the SailPoint platform.
IAM and IAG used to be together till the IAG concept came into being. Converging the two is about creating efficiencies in the process. Integrating the two has proven to be much harder than promised. So yes, I believe any organization with an IAM program will have to tackle this.