Will Role Management become the focus of Compliance?
A few months ago, I wrote a post in which I took issue with the statement that “Role Management will become the focus of Compliance”. My objection kicked off a flurry of responses from various folks, expressing opinions that covered the gamut. I received a lot of responses disagreeing with me, with quite a few of those being from people in the role management business (no surprises there). To be fair though, some of them were quite balanced and articulate.
Maarten Stultjens (of Bhold company, which is a vendor of RBAC solutions) agreed with Roberta that role management systems will become the central point of compliance shortly. But he further qualified his perspective: “of course (this is) ‘only’ with regard to authorization management. The main reason for this is not so much the IT perspective Nishant is mentioning in his blog, it is the business perspective which is driving Role management systems. To find patterns and get these approved via attestation is an IT perspective towards authorization management.”
Now, one thing I take great pride in is my being able to always maintain a business perspective of the IAM problem. I have never thought of it as an IT problem (but one that requires and impacts IT infrastructure). So I promptly challenged Maarten to duel for besmirching my reputation (Just kidding).
Maarten further elaborated: “The main reason why role management systems are so important to achieve compliance with regard to authorization management is that role management systems are able to (1) store and maintain the company policies and (2) enforce these policies (through provisioning engines or manually) and (3) audit if the policies are actually implemented. Compliance is all about ‘defining a policy’, ‘enforce the policy’ and ‘proof that the policy is implemented’. There is nothing to audit when there is no clear policy. Sometimes we – IT people – overrate ourselves by talking about compliance and audit. This is the job of auditors.”
Again, I have no argument with the statement that RM systems are “important” to achieving compliance, just with the notion that they are the focus. Roles have long been viewed as the Holy Grail of IAM – true role-based identity management will solve all problems. But like the Holy Grail, it is really hard (nearly impossible) to achieve. So I tend to have approach blanket statements with some perturbation. I don’t disagree with Roberta or Maarten on how important role management is to compliance. I just want the message to be balanced, and not get exaggerated to the status of “all important”.
Looking at Maarten’s position, I agree with point (1), but disagree with (2) and (3). RM systems will not be able to do those because they present only a partial picture of the reality of a business. If I can simplify an example to make my point, it is fairly common for people to be given privileges in an ad-hoc, but entirely proper, manner. This is invariably done through a request-based, approval enforced mechanism that today is handled by provisioning systems (OIM, for instance). These privileges are therefore out of policy, yet are not exceptions. And a role management system should not have to deal with this kind of scenario (even if it could).
Yes, compliance is the job of the auditor, but an auditor is only as good as the tools they are given, which is where the various IAM solutions come in. Some auditors use audit management software to complete tasks when it comes to their jobs. Auditors care about the roles because knowing the roles a user has tells them about what access the user has and does not have. But they also care about the out-of-policy privilege grants, and want to know that the correct procedures for approving, tracking and attesting those privileges are being followed. They care that audit trails are being maintained, and that there are no loopholes in the business processes.
Another person sent me an email saying “Role management is vital method to achieve compliance while user provisioning is a method to deliver proper user- and permission-information to distributed environments and applications. (yes, UP also collects information from distributed sources for the centralized Role Management)”. This points out one of the main misconceptions that I have been trying hard to fight, and which is probably at the core of the misunderstanding of the space. Too often, provisioning is viewed simply as (to quote) “the bus to deliver this user-permission information, with all required attributes, to all those environments where it is needed.” This really is the IT-centric view. Provisioning systems today (OIM in particular) are actually much more of a business solution than an IT solution, providing rich policy definition and enforcement, and end-user and administrative request-based, approval driven tools for managing privileges in a fluid business environment.
To me, role management is an essential part of IAM. In fact, in today’s environment it is probably the most important part of a compliance-driven IAM solution. It should not, however, be the focus of a IAM-based compliance project. Any good IAM strategy must be a mix of role-based, rule-based and request-based management (think of the old 80-20 rule, just broken down to 50-30-20), with a good overlay of audit and compliance tools. At Oracle, we feel that Identity Administration, Provisioning and Role Management are the three pillars on which (the newly emerging) identity GRC tools are overlaid to provide the foundation of a good identity audit and compliance practice.
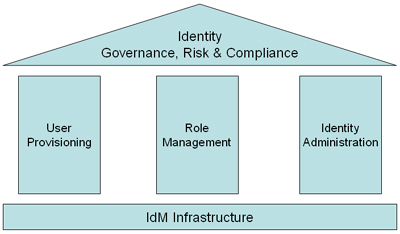
(Of course, knowing how IAM is constantly evolving, I am sure we will be adding more “pillars” to this diagram soon, so take this position with a pinch of salt)
This is driven by the reality of modern business – one that is fluid, ever-changing and way too complex to only codify in the structured system that role-based management represents. Over the last few years, I have dealt with a number of customers that have made the effort to incorporate role management into their IAM projects. Invariably I encountered the following:
- No one agrees on the definition of a role
- Most of them only manage to use roles in a limited manner
The mantra of the day is balance. I think Dave Kearns response to my post was best: “While I do agree that RBAC is the ‘wave of the future’ and is, indeed, necessary to good IdM and compliance, I think of it as being one of the foundations of compliance, not the tool that compels or insures compliance. And certainly not a tool for attestation…”