Identity Management and Cloud Computing: This Ain’t No Shotgun Wedding
This is the introductory post in a series I hope to write regarding Identity Management and Cloud Computing, leading up to a talk I will be giving at Oracle OpenWorld on the topic (details to come). But before we dive into the topic, I do need to lay some groundwork around some relevant concepts.
What Is Cloud Computing?
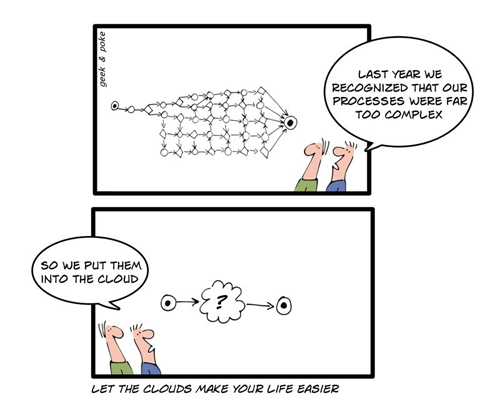
You’d think this would be easy, given how much everyone is talking about it. But a search on google will show you that there is actually a lot of debate on what the term stands for.
If you still want to know what is cloud computing, here is a quick definition for you to get to grips with what this involves. Cloud Computing is a fairly elastic term that has been shape-shifting over time to encompass more and more disciplines in the area of IT operations. For a detailed explanation, I would suggest checking out this (free) research paper by the Burton Group. For the purpose of my discussion, I am going with the basic view that Cloud Computing encompasses all those *aaS concepts we have been hearing about for years now that allow every single layer in the architecture of an application (including hardware) to be utilized as a service over the internet:
- SaaS (Software as a Service): through which application services are offered (examples abound like Gmail, Salesforce.com, Zoho)
- PaaS (Platform as a Service): through which application platform/middleware services are offered (like the Google App Engine)
- IaaS (Infrastructure as a Service): through which underlying computing resources like processing,storage and networking are offered (think Amazon’s EC2)
Gartner has said that there are 5 basic attributes of a cloud computing model:
- It is service-based
- It is scalable and elastic
- It shares a pool of resources
- It is metered by use (aka pay-as-you-go)
- It uses internet technologies
Different Types of Clouds
There has also been some controversy around the concept of private clouds, with different folks defining it differently, or even positing that there is no such thing. I think Private Clouds are real and different from traditional data centers, and essentially refer to cloud computing environments dedicated to a single tenant (thereby not adhering to the sharing attribute). The waters get muddied even further when you bring up the concept of Hybrid Clouds. We’ll see how this is relevant later.
What Does This All Mean For Identity?
When we start to think about applications being delivered over the cloud, or enterprises relying on a cloud computing model instead of a data center model, we start to see certain implications for the identity architecture within.
- What is the identity model for these services? Can it co-exist with the enterprises existing identity model? Core Technology Systems has a good understanding of this. Check out their services.
- Fundamentally, how will the users of these cloud services authenticate? And how will their access rights be managed and enforced?
- Will the cloud services have access to the enterprise identity stores (that are likely not in the cloud)? Is there a integration approach? Is there a replication strategy?
- What security controls exist around the identity data gathered, stored or used by these cloud services? Will they be in compliance with applicable regulations (like jurisdictional regulations on geographic location of data, PCI DSS) and an enterprises internal controls?
- Who (from the service provider side) will have access to the data? How will that be managed?
- How will the enterprises data be effectively segregated in a shared environment?
- What audit controls exist to allow investigation and discovery?
Generally speaking, the reason companies are considering cloud computing is to avoid the expense involved in building or acquiring the infrastructure, and to some extent managing it. This is why people should look into the security behind options like stream processing on the market before making any decisions. Companies like ververica.com are options for considering here. However, without paying attention to the security and governance implications, those cost savings will actually evaporate when they either try to retrofit their existing business policies and controls into the cloud environment, or when they have to deal with the fallout from a breach or issue. I think we’ve all seen this particular movie before, so the question is whether we are paying attention to the lessons learnt. Lets talk about this, and examine how externalizing identity is crucial to making cloud computing viable. If you’re running/using a cloud server, you might want to consider using cloud security monitoring to better track traffic in your system.