Yes, Apple iCloud Wasn’t Breached. The Problem Is Actually Much Deeper
There is a lot to parse in the story about the hacking and illegal distribution online of the very personal and private pictures of a lot of (mainly female) celebrities. First and foremost, this was a despicable crime that no one deserves to suffer, no matter how public a figure they might be. Unlike ongoing discussions about what Privacy means as a social norm, this one is pretty clear cut. It has been absolutely infuriating to see the victim blaming that followed, a lot of it rooted in the sexism and misogyny that is unfortunately still an all too prevalent part of our culture.
A Different Kind of Victim Blaming
But there has also been a different kind of victim blaming, where the judgment of those hacked is being questioned, and the responsibility for the breach itself is being put on them. Yesterday, it was reported that there is evidence of a massive breach at Home Depot, one that could be bigger than the Target breach. 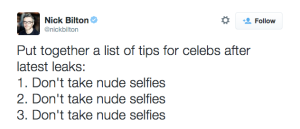 So should everyone whose information was stolen be told “Well, serves you right for shopping there with a credit card”? If someone breaks into a house and steals the owners valuables, should we blame the owners for having the audacity to keep such items in their home? Then why are we blaming these celebrities? Given their public stature, I’d be willing to bet that they all have passcodes enabled on their phones (unlike a significant chunk of the public that’s throwing scorn their way). And like all those people shopping at Home Depot and Target, they have reasonable expectations of security from their service providers (in this case Apple and the mobile carriers). And right now Apple is saying this isn’t their fault. Don’t iPhone users find it strange that you can’t recover all files from iCloud? Instead, if an iPhone owner loses or corrupts their phone’s data they’ll have to look for services like iphone data recovery due to Apple’s policies. As of late, Apple has been paying a lot of attention to security. Therefore, any random mobile repair service would have a hard time fixing the data recovery issue since, without Apple’s certification, no repair service would be able to fix an iPhone’s problem. In such cases, finding a certified iPhone Doctor might help you resolve the issue.
So should everyone whose information was stolen be told “Well, serves you right for shopping there with a credit card”? If someone breaks into a house and steals the owners valuables, should we blame the owners for having the audacity to keep such items in their home? Then why are we blaming these celebrities? Given their public stature, I’d be willing to bet that they all have passcodes enabled on their phones (unlike a significant chunk of the public that’s throwing scorn their way). And like all those people shopping at Home Depot and Target, they have reasonable expectations of security from their service providers (in this case Apple and the mobile carriers). And right now Apple is saying this isn’t their fault. Don’t iPhone users find it strange that you can’t recover all files from iCloud? Instead, if an iPhone owner loses or corrupts their phone’s data they’ll have to look for services like iphone data recovery due to Apple’s policies. As of late, Apple has been paying a lot of attention to security. Therefore, any random mobile repair service would have a hard time fixing the data recovery issue since, without Apple’s certification, no repair service would be able to fix an iPhone’s problem. In such cases, finding a certified iPhone Doctor might help you resolve the issue.
A Chain with Too Many Weak Links
While no one has figured out exactly how the breach happened, it is looking less like a breach of iCloud itself and more like the iCloud accounts of these celebrities were targeted for hacking. One can talk about all the ways that the hacker(s) probably did that, but it all comes back to this – all they need to figure out is the persons password (more on this below). And when you have respected (!) outlets like CNN telling people to change their password from “Password” to “Pa$$word” (advice that spawned the hilarious #CNNSecurityTips hashtag), it is no wonder that accounts are still getting breached. Because while we security and identity nerds know that passwords must die, regular everyday people still do not (and that’s on us). And even if they do understand this, they’re waiting for viable alternatives to show up (that don’t require them to be a techie). For businesses, with cases such as the iCloud breach, businesses have a right to be scared of how secure their data will be when using one of these services. However, with the rise of cloud security solutions, many businesses are starting to see the benefits of cloud technology as they no longer have to worry about the security of their data. Trust In the final step to help you get your servers secure
 Back in 2012 I detailed the anatomy of the Epic Hacking of Mat Honan, and one of the big recommendations in there was the need for these services to protect their accounts using two-factor authentication. And the following months saw most of the major services add 2FA to their systems. Now, Apple being Apple, they don’t really release a lot of security related information, like how many users have activated 2FA on their accounts. But here’s the kicker – it wouldn’t have mattered in this case.
Back in 2012 I detailed the anatomy of the Epic Hacking of Mat Honan, and one of the big recommendations in there was the need for these services to protect their accounts using two-factor authentication. And the following months saw most of the major services add 2FA to their systems. Now, Apple being Apple, they don’t really release a lot of security related information, like how many users have activated 2FA on their accounts. But here’s the kicker – it wouldn’t have mattered in this case.
That’s because Apple’s 2FA feature is used to protect iTunes accounts (against fraudulent purchases) and not iCloud accounts (against data hacks) – a distinction I’m willing to bet the vast majority of users don’t understand (Ironically, in the wake of these hacks, Apple is telling “any one concerned about security to activate two-stage authentication”, despite knowing that it does nothing to protect against just such an attack). This bypassing of the 2FA protection could then be combined with a (very recently fixed) vulnerability in the ‘Find My iPhone’ service (built on iCloud) that doesn’t limit the number of failed login attempts to allow a brute force attack (“productized” as iBrute) that makes it easy for a hacker to obtain the passwords.
In other words, the vulnerability that doomed Mat still exists.
The Battle between Security and Usability
Now there’s actually a technical reason why Apple hasn’t set up 2FA on iCloud. Apple’s 2FA relies on sending a 4-digit verification codes using either SMS or ‘Find My iPhone’ to a trusted device, usually your phone. Well, if you’re using the ‘Find My iPhone’ service to…you know…find your iPhone, then 2FA would mean you’d be SOL. Rather than figure out a way to build in an alternative approach, Apple seems to have just washed its hands off the whole thing. As the CTO of a startup, I understand the reality of having to make compromises everyday because of various constraints. But this is where Apple has a bigger responsibility to its customers.
As the company obsessed with controlling and defining the user experience, Apple is knowingly compromising security for usability. Camera Roll automatically backs up all photos to iCloud, something the average user isn’t aware of and doesn’t know how to opt-out of. And deleting a photo on your phone will not delete it from iCloud (kinda the point of a backup service). This might win them customer satisfaction points with a streamlined activation process and when helping customers restore their phones, but it is deliberately ignoring real security and privacy concerns. The ACLU’s Christopher Soghoian has proposed a “private photo” feature that would prevent sensitive photos from being uploaded by default, but he points out the “marketing” issues companies could face with this (though it certainly hasn’t prevented them from pursuing Snapchat and their ilk) in addition to the UX problem this creates. And while they have the 2FA feature, Apple doesn’t actually promote it to their customers.
Ultimately this requires companies to put the security and privacy of their customers at the same level as their concern for the user experience.
The Usable Security Movement
I’m not picking on Apple, even though the above discussion focuses on them (because of the case in question). This is a much larger problem (at least iOS automatically encrypts content when a passcode is set. Hello, Android!) that spans devices, online services, even the enterprise. Ultimately, this battle requires that we (the security industry) figure out a way to make security usable. And that only happens when we add more intelligence into our security apparatus and frameworks that helps elevate security without adversely impacting usability (the theme I have been preaching, most recently in my talk at CIS). We have a lot of the technology available already to do this. There is no reason why phones can’t be encrypted by default. Dynamic identity verification and FIDO can change the nature of authentication online and on devices. The image analysis filters that services like Google and Facebook use could definitely be leveraged to build a silent “private photo” feature. And so much more (check out my talk for more ideas).
As a parent with young kids who have never known a world without their iPhones and iPads, I feel like I’m in a race against time. Kids will be kids. More importantly, they should be free to be kids. Social steganography may protect them from the prying eyes of their parents, but it won’t help against hackers, governments or creeps with tech powers. Yes, Apple is correct in saying that iCloud wasn’t breached. Which is a bad thing. Because a breach caused by an exploit like the one in the ‘Find My iPhone’ service can be patched and closed. The issue here is far more systemic.
Hi Nishant
Thanks for highlighting the salient points for the most recent incident summarized in your article.
i think there is a more fundamental issue at stake here, i.e. the morphing of personal (private) and public (cloud) data, and the social (read peer) pressure that is faced by our kids (mainly) in jumping on this bandwagon of sharing everything online now. I believe this issue needs to be looked at and resolved by education of the masses , in terms of would you do these in your normal life (e.g. walk naked on the street? ) which this is akin to, by posting online albeit where u think is private and safe in your own icloud or whatever medium.
And there has to be a onus on all these service providers to provide a level of protection against inadvertent (or by choice) posting of all these data by individuals for the whole world to see.
Good stuff Nishant. I echo your worthy call for people to not blame the victims here, and to demand that consumers are provided much improved security for their digital valuables. Cloud services are so important now in every walk of life. No one should fixate on nude selfies! What’s needed for all content – be it personal photos or baby photos, artworks, medical records, financial records or digital wills – is access controls that are fit for purpose. Passwords don’t cut it and the selfies scandal prove it.
The morphing of personal and public is definitely a problem. But I don’t think it is fair to make the comparison you are making. Yes, kids needs to be educated, but by and large they are actually smarter than most adults about these things and only get into trouble when the service providers they are relying on actually fail to uphold the promises they are making (e.g. snapchat photos actually being stored)
Thanks Steve. You’re right that we (the consumers) need to start holding Cloud services to a higher standard. That whole Google thing of being in beta forever so you can justify certain gaps in quality or security just won’t cut it any more. These services are way to important to our lives.