Future in the Clouds? How About Some ESSO-To-Go?
There is little doubt any more that the cloud revolution is in full swing. Enterprises today are adopting cloud-based and hosted solutions for everything from CRM (even industry-specific solutions like this car dealer CRM) to personal productivity applications to business intelligence. Enterprises want the user experience of accessing SaaS applications to be secure, but transparent. This pretty much mandates an approach based on single sign-on technology – one that extends the single login experience that exists within the enterprise to all these third-party resources. Businesses like the hospitality and food industry are incorporating these latest technologies to deal with online activities and store data on the cloud. Software like a motel management system or booking app can ease the workload and manage reservations, organize and shuffle bookings, record payments, generate guest profiles to create the list of regular customers, etc. These resources can increase the efficiency of a business and its popularity as well.
But there is a catch. One of the benefits that enterprises frequently consider when going with a SaaS application is the fact that the user does not have to be within the corporate network to access these systems. These systems can be accessed from any computing device, so long as it has an internet connection. Certain organizations might also deploy privileged access management software to their operations so that privacy is maintained at all times and no one has access to private information. It could be the computer in the hotel business center or a laptop borrowed from a friend. But in an SSO-protected world, no one knows their application-specific passwords anymore (by design). So how can a user access the SaaS application if they do not know their password?
Yes, I know that we want to kill passwords (multiple passwords, to be precise. And I am all for it). But the day when enterprise will allow users to come in and use their own OpenIDs is still somewhere in the murky future, and we need a more practical solution pretty much right now.
Businesses that require SaaS websites or software solutions to operate in the way they intend may want to get in touch with experts at a professional digital products studio; see here to learn more about one such example – https://www.expedition.co/blog/best-saas-websites.
Single Sign-on From Anywhere, To Anywhere
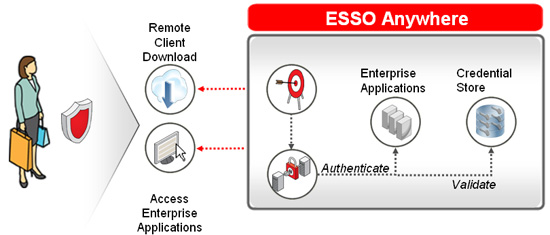
December was a heavy travel month for me, between work travel and vacation, and I actually encountered this problem a couple of times. So I thought I’d use my first post of 2011 to highlight this very real challenge that enterprises are starting to face, and describe a little known solution we have (thanks to the Passlogix acquisition). Oracle Enterprise Single Sign-On Suite Plus or Oracle ESSO (formally Passlogix v-GO) provides seamless SSO to a wide range of enterprise resources through the use of a desktop agent that manages all of the user’s account names and passwords on their behalf. Applications, including SaaS and Web resources, are recognized when they are launched based on their unique attributes, and the correct access credentials are supplied to each as required, transparent to the user.
Oracle ESSO solves the specific challenge posed above through on-demand functionality called Oracle ESSO Anywhere. When deployed, ESSO users can download a transient version of the agent by clicking on a website link. The user is now able to access the SaaS applications with the same protections afforded by the permanently installed agent inside the enterprise. An added benefit is that this also helps protect against users exposing passwords to threats that capture input directly from the keyboard (keyloggers). When the agent is shut down, the on-demand software removes all traces of the ESSO application and the user’s application credentials, ensuring that security is maintained.
Cool, right? I wish there was a personal edition of this that I could use for all my web-based services. This also highlights another aspect of identity management that is top of my mind as we start a new year. Enterprise environments are evolving rather rapidly, so it’s important to make sure that the solutions you deploy can adapt to your changing environment. As access to your resources evolves beyond the desktop to the myriad of computing devices (smartphones, tablets like the iPad, etc) “infiltrating” your enterprise, we’re going to see significant changes to traditional IdM. And that’s a good thing.